With the advent of technology, the number of inventions in the autonomous and connected vehicle industry will increase exponentially to such an extent that manual vehicles might fade out completely. Undoubtedly, connected vehicles have some advantages such as Wi-Fi connection, live music streaming, remotely controlled car operations, and much more.
With so many advantages for connected vehicles, the one disadvantage is cyberhacking. Here are six areas of current and future vehicles that are most vulnerable.
Access via Digital Keys
With remote technology, the vehicles today have digital fobs and wireless keys for locking and unlocking vehicles rather than traditional keys. The virtual keys have a connection with the vehicle through Bluetooth, WI-FI, and Infrared (IR) communication. Hackers extend the wireless signals or hack into IR communication and gain access to the owner’s private information.
Hackers can quickly gain access this way due to the carelessness of the vehicle owner. Owners should set up two-step authentication when using digital keys.
Software Security Vulnerabilities
Any online software can be vulnerable to cyber theft, which is the same for connected vehicle software and a base for autonomous vehicles. If it is weak, then the vehicle could be open to cyberhacking.
Many automakers spend a great deal of time designing safe and secure automotive software, but there are currently no standards in the industry. Sometimes, cybersecurity is an afterthought and should be built from the beginning of the design. Automakers have many reasons for the lack of cybersecurity: quick deadlines, improper programming, lack of verifications, and knowledge base.
Sensor Risks
Every driverless vehicle has a variety of sensors installed. The purpose of these sensors is to identify and navigate on the road, detect dangers while driving, and ensure the utmost safety throughout the drive. Out of all the sensors, the most susceptible to risk are GPS, LiDAR, and IMU.
· GPS Sensors
Connected cars have GPS systems for monitoring and tracking the vehicle. GPS helps guide the vehicle to the destination. Hackers can manipulate GPS signals that receive information via GPS satellites. Hacking a GPS allows criminals to use the data to guide the vehicle accordingly, which can be dangerous for both passengers inside the vehicle and everyone else on the road.
· LiDAR
The Light Detection and Ranging (LiDAR) sensors are specially invented to provide complete visibility of the surroundings for the self-driving vehicles. With the help of LiDAR, the vehicle gets to know the distance of people and objects from itself. The fraudsters gain access to the sensor and send similar signals and confuse the vehicles. As a result, cars fail to recognize the exact distance from the object, and this often leads to accidents.
· IMU
The Inertial Measurement Unit (IMU) sensor helps in locating and positioning the vehicle no matter where it is. The device helps in telling what is going outside of the vehicle, keeping in view the interior. Malicious attackers often gain access and misguide the car by giving false signals to the vehicle.
Cloud Security Threats
Autonomous and connected vehicles store a lot of information on the cloud. As these vehicles are self-driving, all the data necessary for operating is saved in the cloud.
For proper functioning, there is a continuous exchange of data to and from the cloud. Hackers can gain access to the information being shared to the cloud as they are aware of the data systems. These people even threaten the data center authorities to get sensitive information about the vehicles through the cloud-based system. Mostly, hackers make use of this information to manipulate the safety-critical systems of vehicles like cruise, brakes, steering, etc.
Malicious Network Attacks
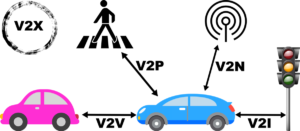
The network of connected vehicles is at high risk. Hackers get into cellular networks like Wi-Fi, LAN, and other connections. The three main types of network thefts include:
- Vehicle-to-everything (V2X)
V2X helps in connecting the vehicle with everything that might affect it, such as traffic signals, other cars, etc. Attackers exploit the bugs present in the protocols used for V2X networks (Wi-Fi, GSM, and Bluetooth).
- Vehicle-to-Vehicle (V2V)
These types of networks connect the vehicles by exchanging information on speed, location, directions, brakes, etc. The hackers get access to the insecure protocols of V2V networks and receive personal information of other vehicles.
- Vehicle-to-Infrastructure (V2I)
The network established between the vehicle and the infrastructure of the road is known as V2I networks. The attackers can get the signals of these networks and make use of the information for crime easily.
Attacks on Auto parts
Auto parts, like the Engine Control Unit (ECU), are often hacked. The system is responsible for enhancing the safety of the vehicle. However, the attackers change the information on the ECU and get access to all the private information, for instance, passcodes, security keys of the vehicle, etc.
Similarly, another way to get access is by onboard diagnostics (OBD). The hackers make use of the device to add unnecessary information in the vehicles’ network and manipulate it according to them.
Final Thoughts
The connected computer and network systems increase the chances of cyber risks that can even lead to fatalities. Therefore, people need to know what they are risking when they are accessing autonomous and connected vehicles. This way, vehicle owners will be able to take all the measures to protect their privacy and safety beforehand.
Tristan Zheng is a big automobile and sports fan. Currently, he is working as a contractor for Riders Share, a motorcycle rental platform that allows users to rent out their motorbikes for money.
Editor’s Note: The opinions expressed in this article are those of the author.
Photo attribution: Vehicular Communication licensed under the Creative Commons Attribution-Share Alike 4.0 International license.